Keeping yourself safe from Cyber Crime – words Alan Woods
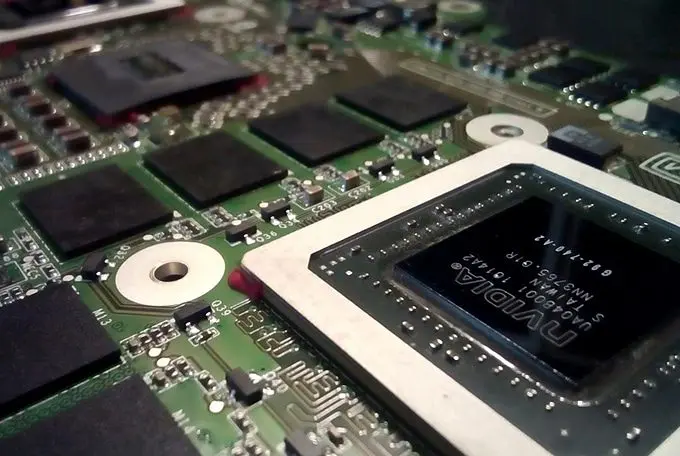
 “cybercrime” (CC BY 2.0) by Infosec Images
“cybercrime” (CC BY 2.0) by Infosec Images
As we spend an increasing amount of our lives online, the need for internet security has become even more vital. Increased screen time inevitably equates to a greater exposure to threats of infection or malicious attack of a more targeted variety.
For our personal use, we may now routinely buy software packages that promise to deliver firewalls and anti-viral capabilities, but for organizations large and small the threats are even greater and so, inevitably, is the requirement to keep ourselves safe from Cyber Crime.
The UK’s official crime statistics, as compiled by the Office for National Statistics, included cybercrime for the first time when they were published last October. The inclusion of online offences saw the overall figure more than double – up to 11.6 million attacks – of which no fewer than 5.1 million were identified as cybercrimes.
A typology of threats
Online security professionals now categorize different threats according to the type and level of activity they present. RFI (Remote File Inclusion) are used for stealing key data; SQLI (Structure Query Language Injections) enable the hacker to not only view confidential files but also in some cases to delete them or even to take control over them completely. As for XSS (cross-site scripting), it is typically aimed at accessing the confidential data of websites’ customers. At the sharp end of cybercrime is a category of attack that is referred to in generic terms as an Advanced Persistent Threat, or APT.
 “Cyber attacks” (CC BY-SA 2.0) by christiaan_008
“Cyber attacks” (CC BY-SA 2.0) by christiaan_008
Advanced Persistent Threats
An APT is a cover term for a concerted, targeted series of attacks that are designed to establish a long-term invasive presence on a network. A key aspect of APTs is the level of sophistication and expertise involved in their deployment. Each of the modes of attack mentioned previously may be deployed at one time or other. As a result, APTs are most typically used as a means to attack only the largest and hence potentially most valuable sites. This is the big money end of cybercrime, with millions of pounds at risk.
APTs are typically broken down into three phases. These comprise Infiltration, which is gaining access to a network’s files, Expansion within the network as the malicious presence is extended and embedded, and Extraction. Such is the level of sophistication involved that even the extraction phase of the attack may be hidden, and as a result an unwary organization may only discover it has been subject to an APT when it is too late and its data – and that of its clients – has been removed or otherwise compromised.
An Ongoing Arms Race
Nothing in this scenario stays still for long. There is an unfolding global dynamic that marks the development of new threats and new counter measures. Sophisticated security software is now capable of monitoring traffic across servers and identifying any suspicious activity at an early stage. Networks now typically employ access control software that will block anything that either derives from a known malicious source or appears to do so, and so-called white-listing whereby networks are restricted to accessing known, safe domains. As the ONS figures suggest, cybercrime is a real danger to all of us and the government has warned of a new digital crime wave The ongoing arms race between legitimate service providers and the criminals may be being waged largely out of sight, but that does not mean we should ever drop our guard. Awareness of our internet security has never been more vital.
Keeping yourself safe from Cyber Crime – words Alan Woods